PRACTICAL CYBERSECURITY In 2022: Staying Miles Ahead of Attackers By Practicing Proactive Cybersecurity Program. Vulnerabilities , (including devastating ones) aren’t going away anytime soon, so organization’s ultimate win against the adversaries will be owning a PROACTIVE cybersecurity program giving her an upper hand- with Proofs! Attackers targeting organizations does NOT requires any compliance to security […]
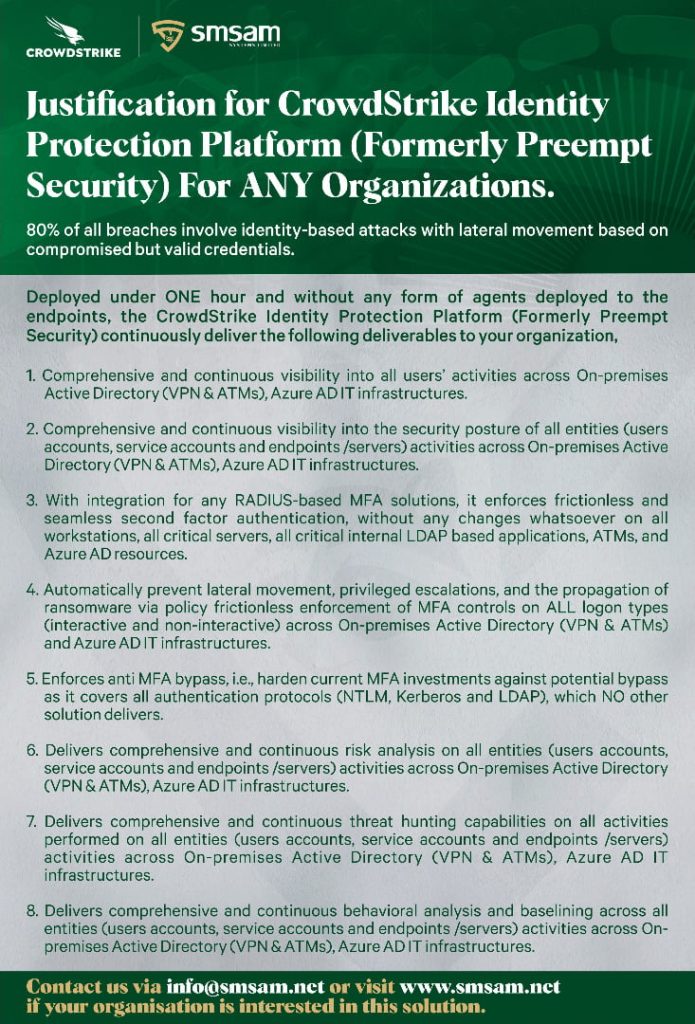
CrowdStrike Identity Protection Platform (Formerly Preempt Security) Capabilities.
CrowdStrike Identity Protection Platform (Formerly Preempt Security) Capabilities. Stopping Ransomware Threats with the CrowdStrike Zero Trust Solution. How To Do Threat Hunting with Falcon Identity Protection. How To Detect and Prevent Lateral Movements with Falcon Identity Protection. How To Detect and Prevent Suspicious Activities with Falcon Identity Protection. How To Enable Identity Segmentation with Falcon […]
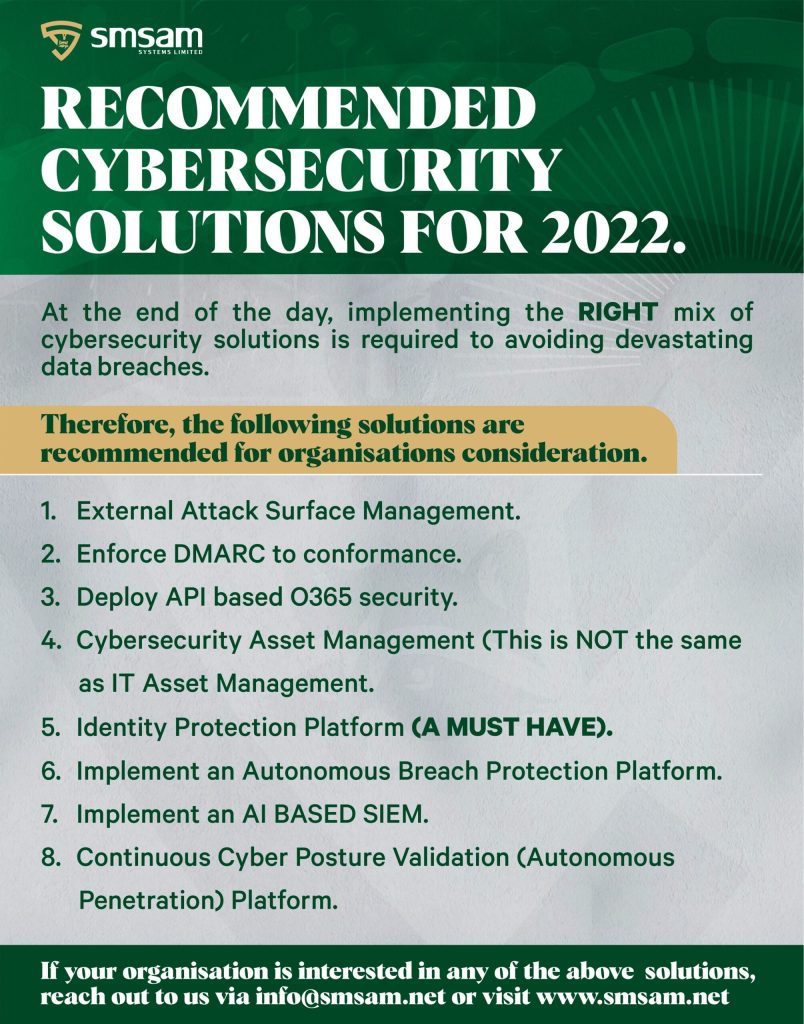
Recommended Cybersecurity Solutions for 2022.
Recommended Cybersecurity Solutions for 2022. Based on threat intelligence gathered from the cybersecurity community on the operations of threat actors (hackers) and malicious insiders, organizations should consider updating their cybersecurity program with the following cybersecurity toolsets. 1- Autonomous Penetration Testing. This is a solution that helps organizations to continuously validate their current cybersecurity posture, i.e., […]
Six Key Mistakes Leading to SOC Burnout
Six Key Mistakes Leading to SOC Burnout. If you work in a SOC in any way, this post is highly recommended for you… Mistake #1 – Underestimating the impact the phishing threat has on your SOC Mistake #2 – Thinking you can’t do better than your existing email security provider Mistake #3 – Thinking all […]
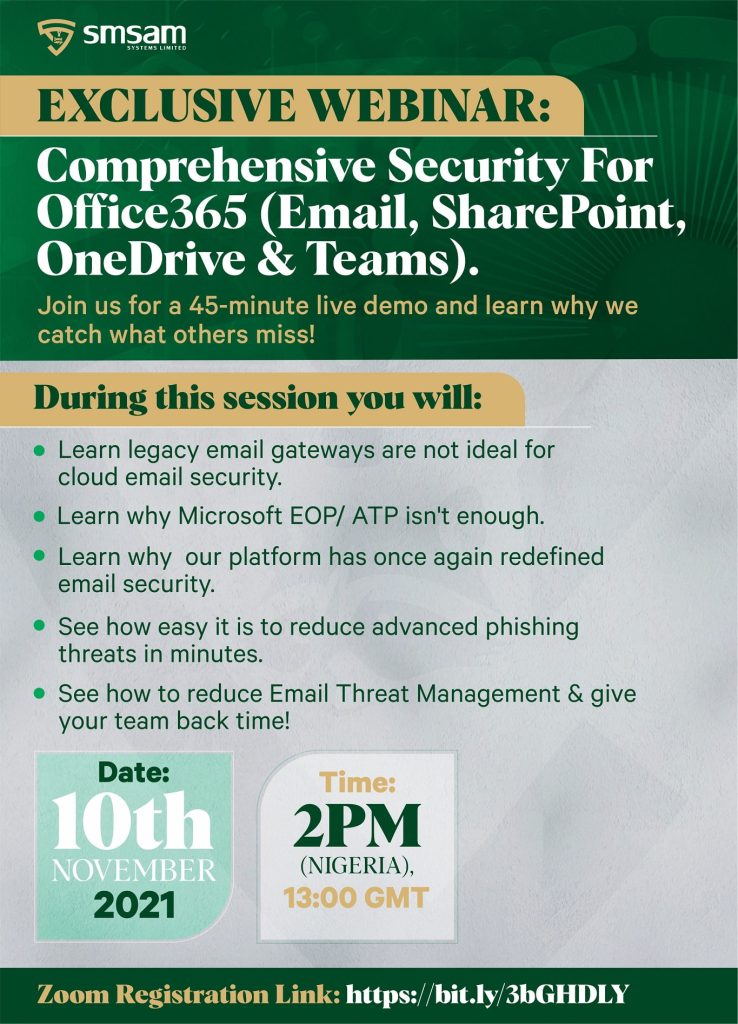
Prevent Malicious Emails From Getting Into Users Mailboxes: Comprehensive Security for Office365 (Email, SharePoint, OneDrive & Teams)
Prevent Malicious Emails From Getting Into Users Mailboxes: Comprehensive Security for Office365 (Email, SharePoint, OneDrive & Teams) If your organization is interested in dramatically reducing phishing attacks and other sophisticated email borne attacks down to as much as 92% (with proofs) then read on.. Consider the following. 1- Do you currently deploy Microsoft EOP /ATP […]
Major Mistakes Leading to SOC Burnout and How to Address Them.
Major Mistakes Leading to SOC Burnout and How to Address Them. SOC Members battle with burnout, overload, and chaos. According to Ponemon Institute– “IT security personnel are approaching burnout as they spend increasingly more time on threat investigation while complexity and chaos, alert fatigue and workload grow.” To be more specific about the burnout to […]