Major Mistakes Leading to SOC Burnout and How to Address Them.
Major Mistakes Leading to SOC Burnout and How to Address Them.
SOC Members battle with burnout, overload, and chaos. According to Ponemon Institute– “IT security personnel are approaching burnout as they spend increasingly more time on threat investigation while complexity and chaos, alert fatigue and workload grow.”
To be more specific about the burnout to the SOC team, Gartner stated the obvious truth in their 2020 Market Guide for Security Orchestration, Automation and Response Solutions (SOAR)- “The most common use case [for SOAR] is automating the triage of suspected phishing emails reported by end users” This happens “dozens to hundreds of times per day” Goal is to determine “whether the email (or its content) is malicious and requires a response.”
From the above, we can safely conclude that the problem with phishing emails is responsible for most of the burnouts experienced by the SOC!
Major Mistakes Leading to SOC Burnout and Recommendations.
1- Underestimating Phishing Threat.
- According to the Avanan’s State of Email Security Survey (https://www.avanan.com/blog/the-state-of-email-security), it was found that managing email threat takes 22.9% of the SOC’s time. That’s 2-3 hours per day.
- Of that time, 47% is spent investigating suspected phishing emails reported by end users.
- 27% is spent responding to actual phishing emailsEnd-users are encouraged to report to SOC.
- Each end-user request takes more than seven minutes to investigate manuallyThis leads to SOC burnout and ineffective responses
2–Can’t Do Better Than Current Security Solutions.
“If [Microsoft, Proofpoint, Mimecast] can’t stop it, who can?” . Legacy solutions were built for legacy world, not API or AI-enabled and thus, less effectiveLess effective email security=more phishing=more SOC work=more SOC burnout.
Legacy email security lets significantly more malicious emails through, both SEGs and Microsoft are bad offenders
More malicious emails increase potential for problems
Recommendation: Do a trial with an inline security provider that can reveal how much your current solution is missing
3- Thinking ALL AI /ML Are Built the Same.
AI and ML are not just labels, they need to actually work. The best AI and ML are trained on the best datasets
The only way to do that is be inline, i.e. gives chance to understand who’s being emailed, social graphs, activity with apps and more. Better AI leads to better catch rate and protecting inline leads to better AI
Ask: Can your solution’s AI deliver industry-standard protection today, or is it just in the roadmap?
Avanan can instantly add new, evasive attacks to our AI, allowing us to stop them faster
Stop what other miss—train AI our most sophisticated attacks
Recommendation: Ask: What’s on the roadmap and what’s in use and fully available today?
4- Use Chopsticks to Catch a Fly.
Many orgs are opting to train first, before implementing security. Employee phishing training is essential,It’s not a full replacement for total email security
Recommendation: Reduce attack surface first. Finish it off with comprehensive security training for end-users.
5- Failure to Consider Impact Phishing Training Has on SOC.
When you implement phishing training, especially as your go-to method of prevention, SOCs suffer. In one case, a company saw 16,000 emails reported to the SOC in one month. More end-user reports lead to more work. Each end user report takes seven minutes to analyze, more if it’s malicious and remediation is involved
Recommendation: Implement email security that prevents malicious emails from reaching the inbox.
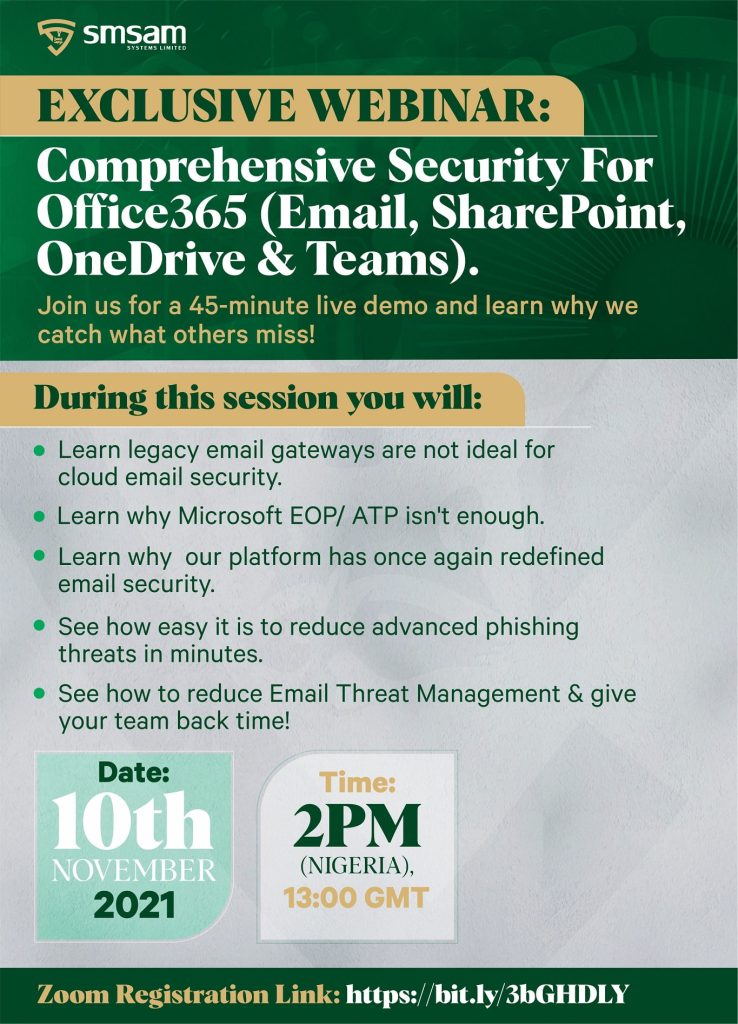
Join our weekly webinar scheduled for this Wednesday , 10th November 2021 at 13:00 GMT ( 2PM- Nigeria) and see how to reduce about 30% workload to SOC by implementing and efficient and effective anti-phishing platform. Register here, https://www.smsam.net/webinars/comprehensive-security-for-office365-email-sharepoint-onedrive-teams/
