Managed SOC Solution Offering
Real time advanced threat detection and auto-remediation with Machine Learning and Artificial Intelligence.
Solutions Components Of SMSAM's Managed SOC Offering
Rather than going through the pains and burdens of procuring multiple solutions to manage your security operations center, our Managed SOC platform is now leveraging the OTM security platform to deliver the FIRST and ONLY natively integrated cybersecurity platform for an efficient and proactive SOC without requiring writing or tuning of rules whatsoever!
Licensing is neither based on EPS nor Bandwidth consumed; hence your entire IT infrastructures (On-Premises and Cloud) are covered with a SINGLE license!
- SIEM – Security Information and Event Management
- UEBA – User and Entity Behavior Analytics
- SOAR – Security Orchestration and Automation Response
- TI – Threat Intelligence
- IPS – Intrustion Prevention Systems
- IDS – Intrusion Detection Systems
- VA – Vulnerability Assessment
- EDR – Endpoint Detection Response
- NTA/NDR. – Network Traffic Analytics/Network Detection & Response
- AI – Artificial Intelligence
- ML – Machine Learning
- DTM – Dynamic Threat Models
- AM – Asset Management
- CCM – Continous Compliance Monitoring
- NBAD – Network Behavior Analytics Detection
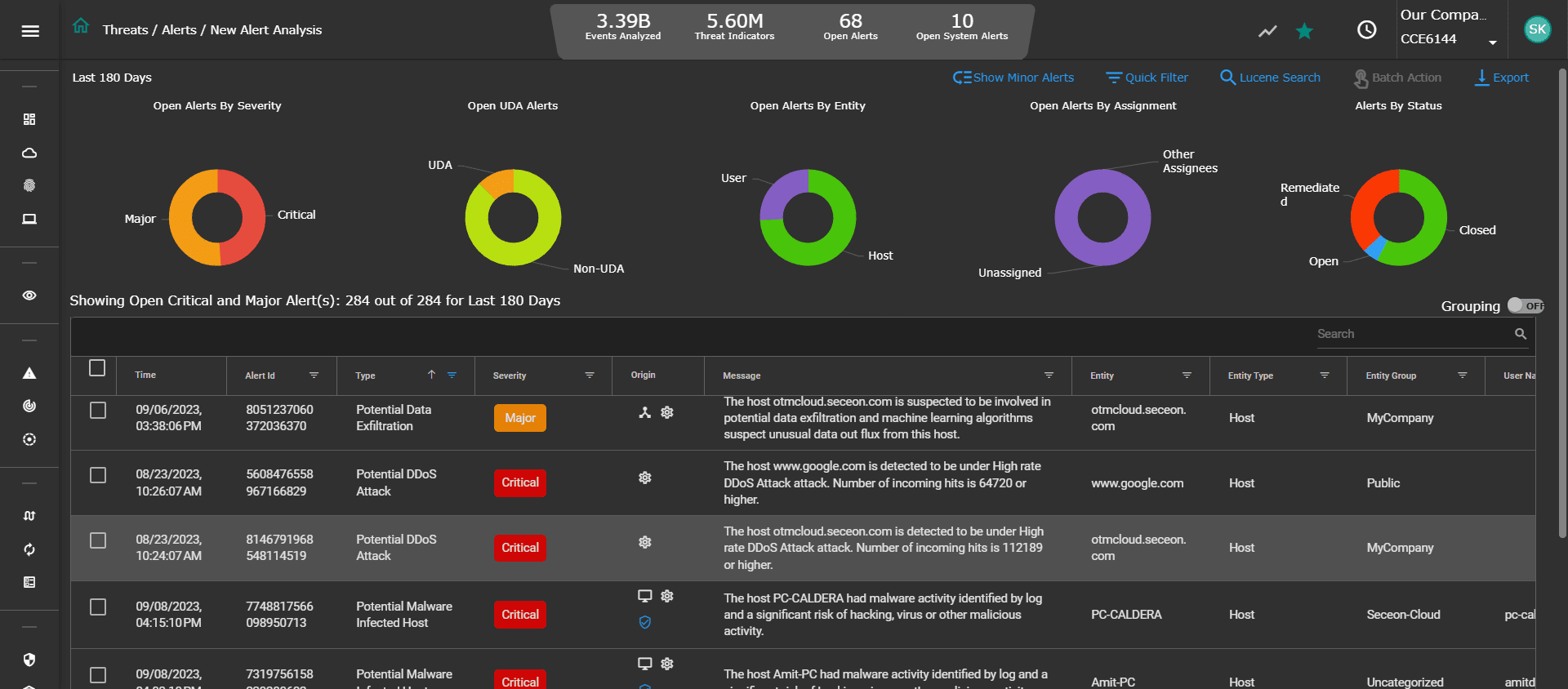
The Alerts Analysis
Get a quick color-coded view of critical and major alerts, along with status, users and hosts – broken down by severity and confidence (score).
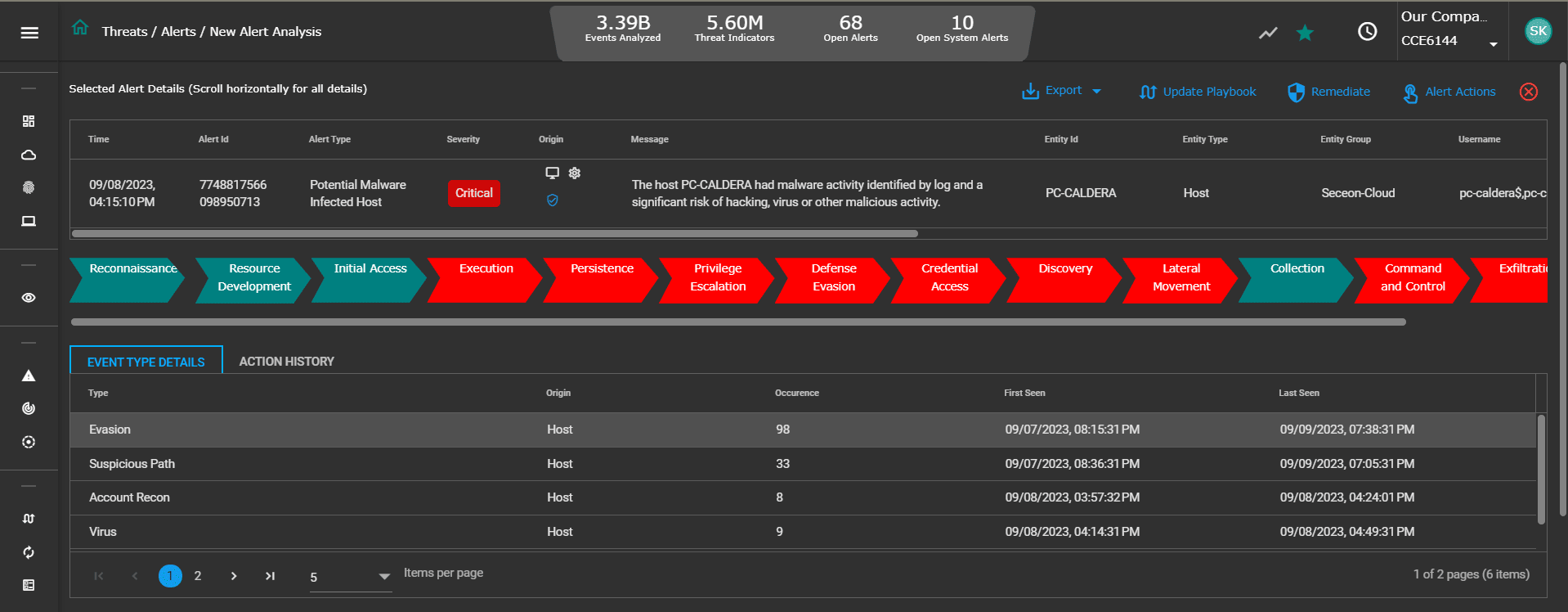
Alerts and Threat Indicators
Understand the nature of alerts and underlying threat indicators, including assets and users impacted. Drill down further to look into the event or network flow attributes (source IP, destination IP, event type, timestamp, process name, etc.)
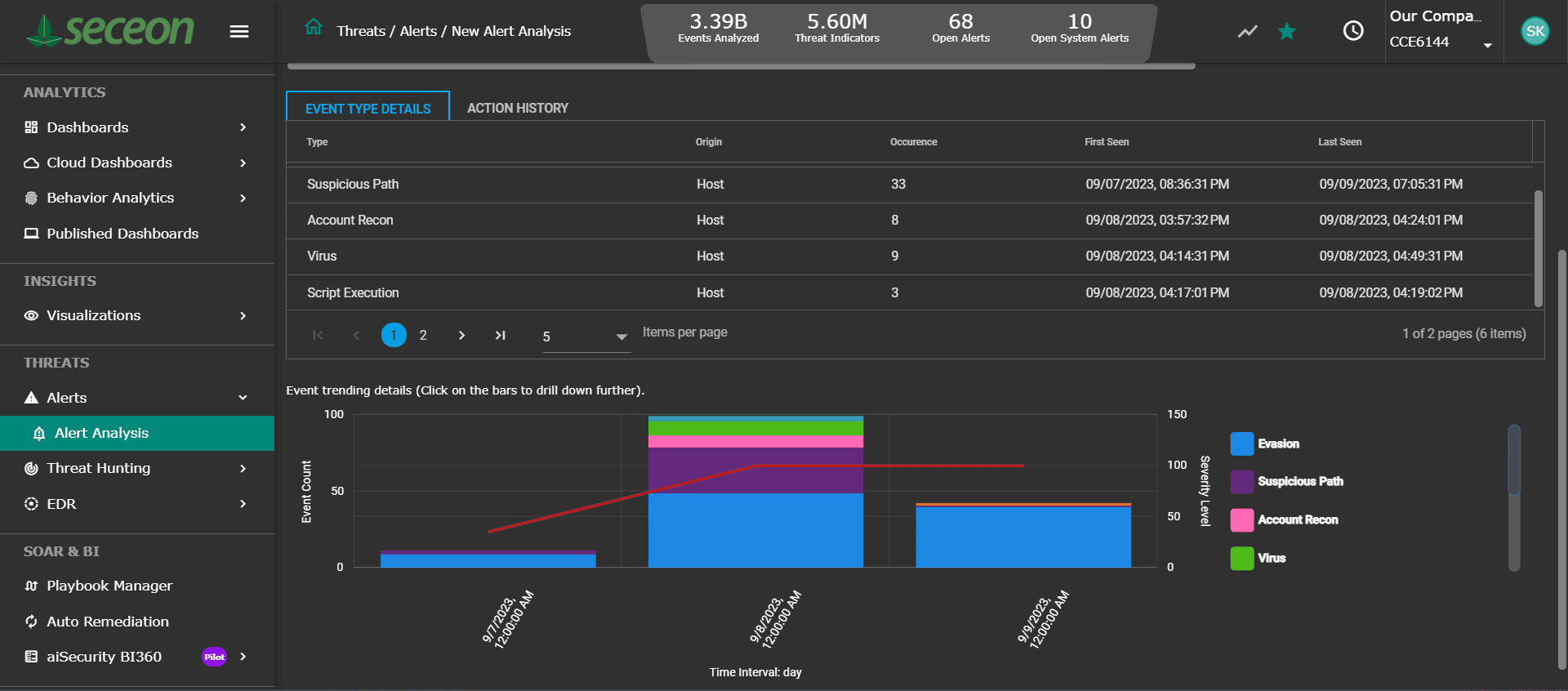
Event Trending
Take a quick view of the evolving threat indicators and number of occurrences over a period in time – broken down chronologically with severity level and confidence score.
Taking radically different approach to cybersecurity
Empowering enterprises to take on the challenges posed by emerging threat vectors, techniques and tactics
