5 REASONS WHY ORGANIZATIONS CHOOSE AVANAN OVER PROOFPOINT, MIMECAST, TRENDMICRO, MESSAGELABS, FORCEPOINT & OTHER ESGs. If your organization is interested in a comprehensive, practical and yet cost effective security of the entire Office 365 ecosystems (Email, SharePoint, OneDrive and Teams) then read this…… Avanan Believes in Defense-in-Depth. SEGs Disable Microsoft and Google’s Default Security. Our […]
PRACTICAL CYBERSECURITY: HOW TO STOP INSIDER THREATS WITHOUT LOGS, NO TUNING & AT AN AFFORDABLE COST.
PRACTICAL CYBERSECURITY: HOW TO STOP INSIDER THREATS WITHOUT LOGS, NO TUNING & AT AN AFFORDABLE COST. Think about the following, 1-Why stop short with just detection, when you can prevent attacks that leverage user credentials? 2- Why burden your SOC analysts with questions on false positives, when most of them can be auto resolved by the user? […]
PRACTICAL CYBERSECURITY: Extending MFA Controls to Legacy Applications, Legacy Network Resources & Administrative Tools!
Legacy apps, legacy network resources, legacy authentication protocols, administrative tools, are part of the network and enterprise operations. For example, Mainframe, HR Systems, Powershell, PSexecare too often excluded from Multi-Factor Authentication (MFA) architecture which makes them the weakest link. Remote Desktop Protocol (RDP) use has exploded in use for work from home employees, and DevOps […]
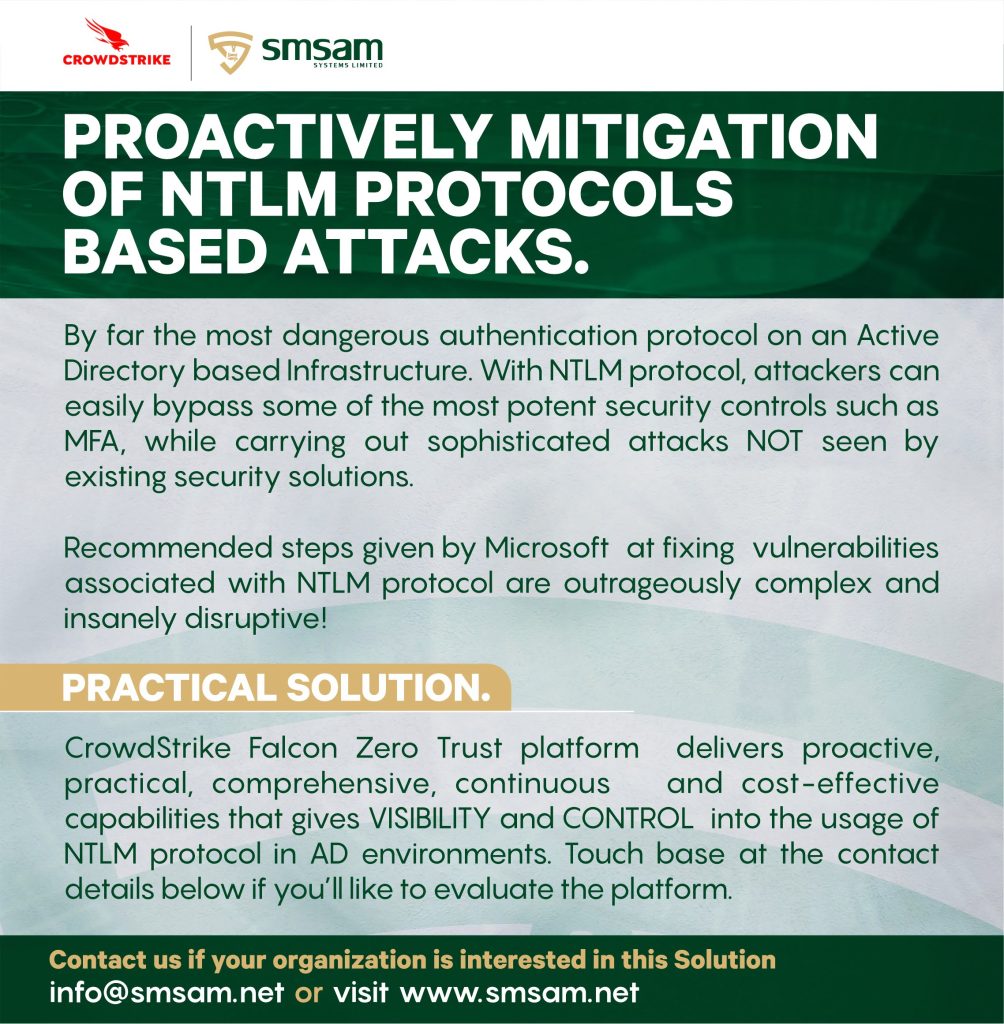
PRACTICAL CYBERSECURITY: Defending Against One Of The Most Sophisticated Vulnerabilities In Any IT Infrastructures.
Vulnerabilities inherent in the NTLM Authentication protocol remains a massive albatross for any Active Directory based Iat infrastructures (about 90% of organizations globally have AD). Most of the sophisticated attacks performed by threat actors leverage NTLM protocol based vulnerabilities and Microsoft has STRUGGLED to get a hand on it! The post referenced here presents one […]
100% AGENTLESS AGENTLESS NETWORK ACCESS CONTROL (NAC) PLATFORM.
Here is an efficient and cost-effective NAC solution for organizations of all sizes. Maintaining regulatory compliance by safeguarding your network doesn’t need to be difficult or expensive.Know and control your network with Easy NAC, the simple and affordable Network Access Control (NAC) solution. Easy NAC automatically discovers devices, profiles them, and controls access to the […]
100% Agentless Network Access Control (NAC) Platform.
100% Agentless Network Access Control (NAC) Platform. A NAC solution that delivers it core capabilities without fuss! See below some of these capabilities. Full visibility of all devices on the network Zero trust, automatic quarantining of rogue devices Alerts to administrators Supports guest access, BYOD, and remediation Collects data from the network Integrates with endpoint […]
Office 365 Security That Works! Complement (Do NOT) Replace Existing EOP /ATP!
Are you considering Proofpoint, Mimecast, TrendMicro, MessageLabs or any other MTA based solutions to secure your Office365 platform? Wait a second and look at Avanan. Contact us if interested. Set up in under FIVE , yes 5 minutes you’ll see how the entire ecosystems of Office365 (Email, SharePoint, OneDrive and Teams) are protected from sophisticated […]
Exclusive: Hackers tried to exploit two zero-days in Trend Micro’s Apex One EDR platform.
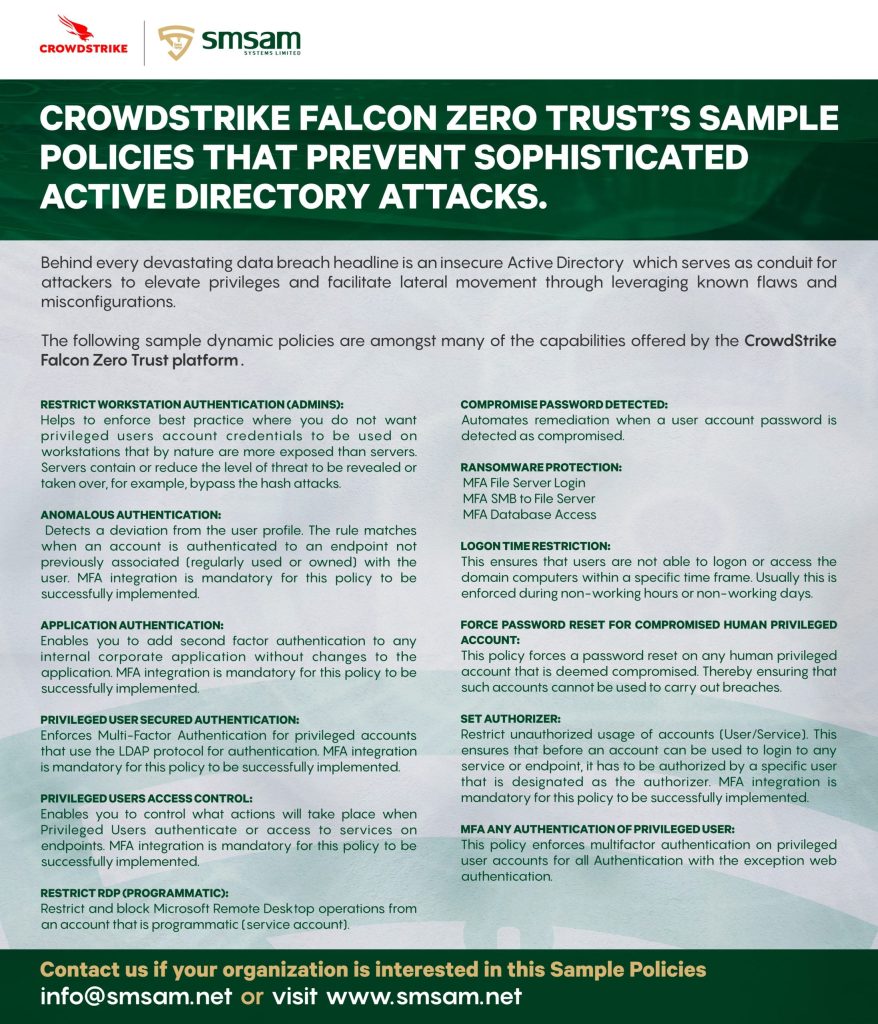
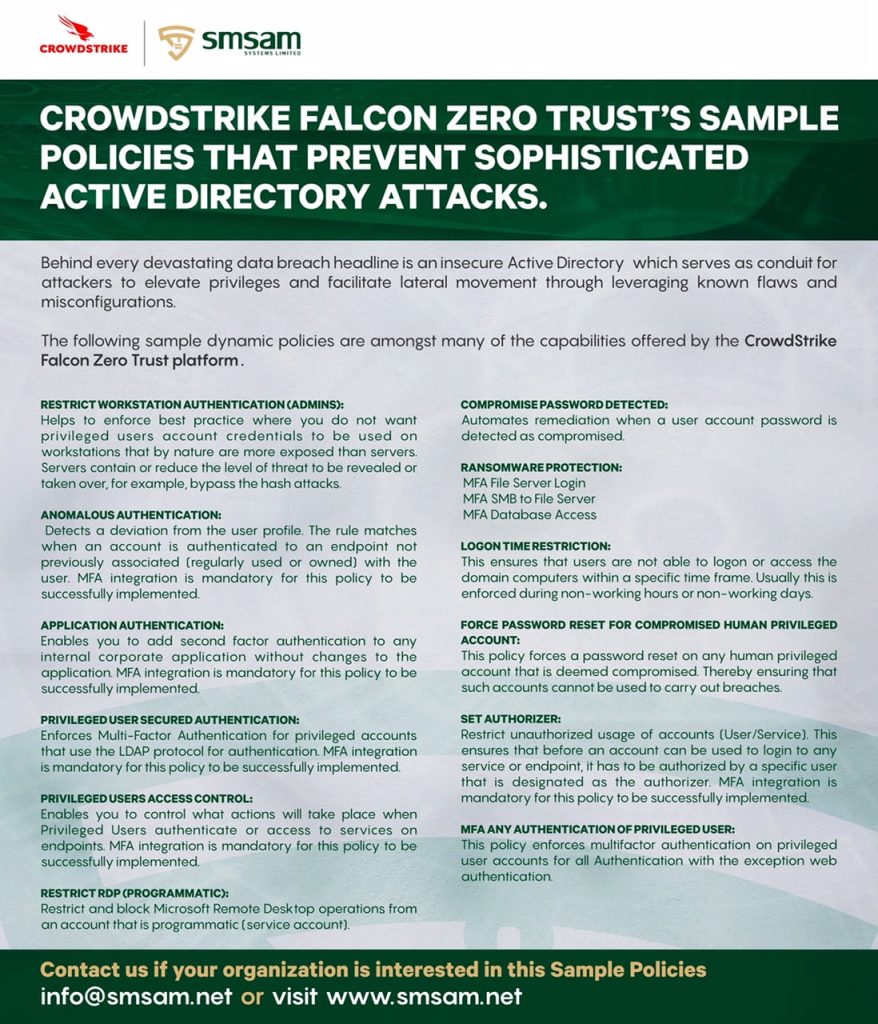
Why Proactive Active Directory Security Should Be Part of Organizations Cyber Defense Toolset. Recently, hackers tried to exploit two zero-days in Trend Micro’s Apex One EDR platform, see this https://therecord.media/hackers-tried-to-exploit-two-zero-days-in-trend-micros-apex-one-edr-platform/ . Now, these sort of attacks is one the core reason why Proactive and Unified Identity Stores security platform is a non-negotiable inclusion in organization’s cyber defense […]
Avoiding False Sense of Security With Current MFA Controls.
There are multiple ways that attackers can BYPASS existing MFA controls once they have a foothold in the internal corporate network. 1- Non Interactive Logon. Authentication to resources using SMB, PSExec and other windows native bypasses many MFA controls.2-Degrading Authentication Protocols. Once an attacker is able to degrade the default KERBEROS authentication to NTLM then […]
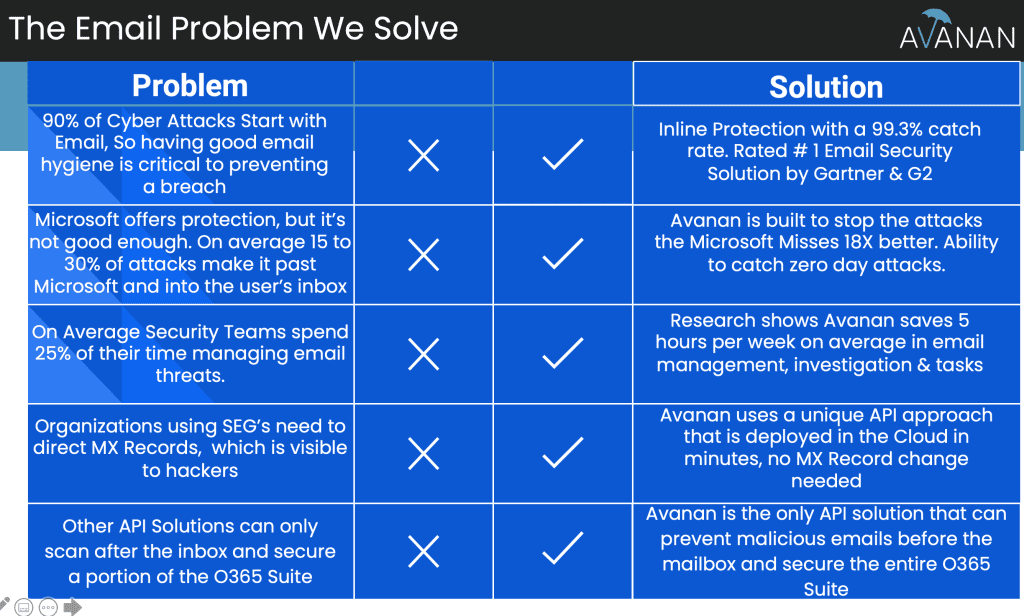
Comprehensive Office 365 Security
The attached imaged contained a summary of how we secure organization’s cloud email infrastructures (Office 365 and G-Suite). For review from REAL USERS, see this, https://www.gartner.com/reviews/market/email-security/vendor/avanan/product/avanan/reviews Why Avanan Platform for Office 365 and G-Suite Platforms? What makes Avanan unique is the fact that we built an architecture designed for cloud email, vs. retrofitting yesterday’s email […]